DevOps Manual
The Software Bill of Materials (SBOM) is a crucial component in managing software supply chain security. It provides a comprehensive list of components, libraries, and modules that are used to build software. SBOMs are essential for tracking the components of software, understanding the relationships between them, and managing vulnerabilities that may arise.
- Assessing and managing the risk of vulnerabilities in software components, ensuring the security and compliance of the software.
- Enabling comprehensive tracking of software dependencies and providing detailed reports on the components used in the software.
- Contributing to maintaining the integrity of the software supply chain by providing visibility into the origins and composition of software components.
- Promoting collaboration and communication among stakeholders in the software supply chain, while also providing a framework for standardizing best practices in software component management.
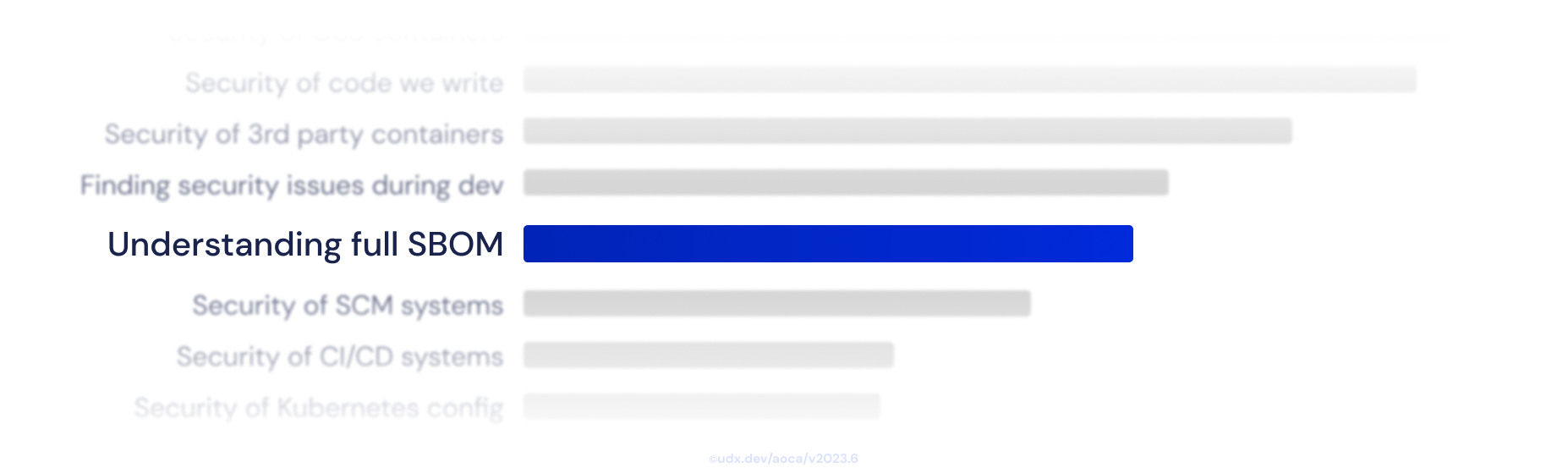
Understanding the full SBOM of your app is a common challenge faced by organizations, as it requires comprehensive visibility into all software components and their dependencies, which can be complex and constantly evolving. However, overcoming this challenge is essential for effective vulnerability management and ensuring the security and compliance of your software supply chain.
An SBOM is akin to a list of ingredients for software. It details every piece of software used, including versions and patches applied. This transparency is crucial for managing vulnerabilities, license compliance, and understanding the impact of software changes. In essence, an SBOM provides a foundation for effective software supply chain risk management.
SBOM plays a pivotal role in software supply chain security. It allows organizations to identify and manage vulnerabilities in third-party components, ensuring that they can respond effectively when new vulnerabilities are discovered. By providing a clear view of all software components, an SBOM enables proactive risk management and enhances overall software security.
Compliance with standards such as SOC-2, PCI, and CMMC often requires a thorough understanding of the software components in use. An SBOM supports this by providing a comprehensive view of software components, making it easier to demonstrate compliance with these standards. It can also support audit processes by providing a clear record of software components and their associated vulnerabilities.
SBOM is not just a static document; it is a vital part of vulnerability management and software compliance in DevOps practice. When properly integrated and utilized, SBOMs play a crucial role in improving software transparency and security.
Modern DevOps workflows can benefit significantly from the integration of automated SBOM integration and scanning tools. These tools can generate and upload SBOM alongside with release artifact and scan it against known vulnerability databases and other security resources to identify potential risks.
Automation ensures that the scanning process is both consistent and efficient, making it easier to track and manage risks over the lifespan of a product.
SBOM generation are useful when developing locally before move the app logic to the remote repository. Tools like SYFT can be used for generating SBOM from container images, filesystems, archives, and more to discover packages and libraries.
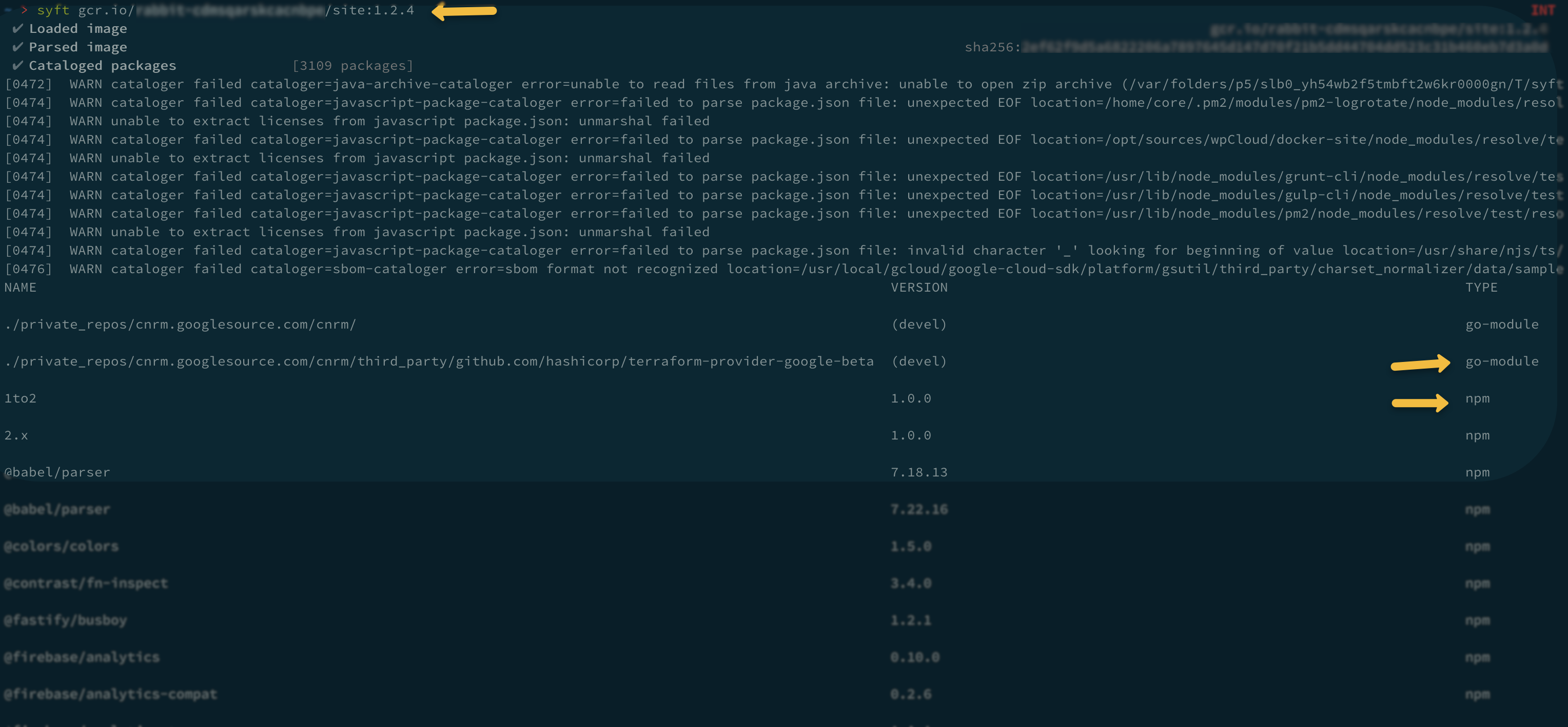
Local Testing Example
Integrate SBOM generation into the CI/CD pipeline. Tools like SPDX or CycloneDX can automatically create an SBOM during the build process.
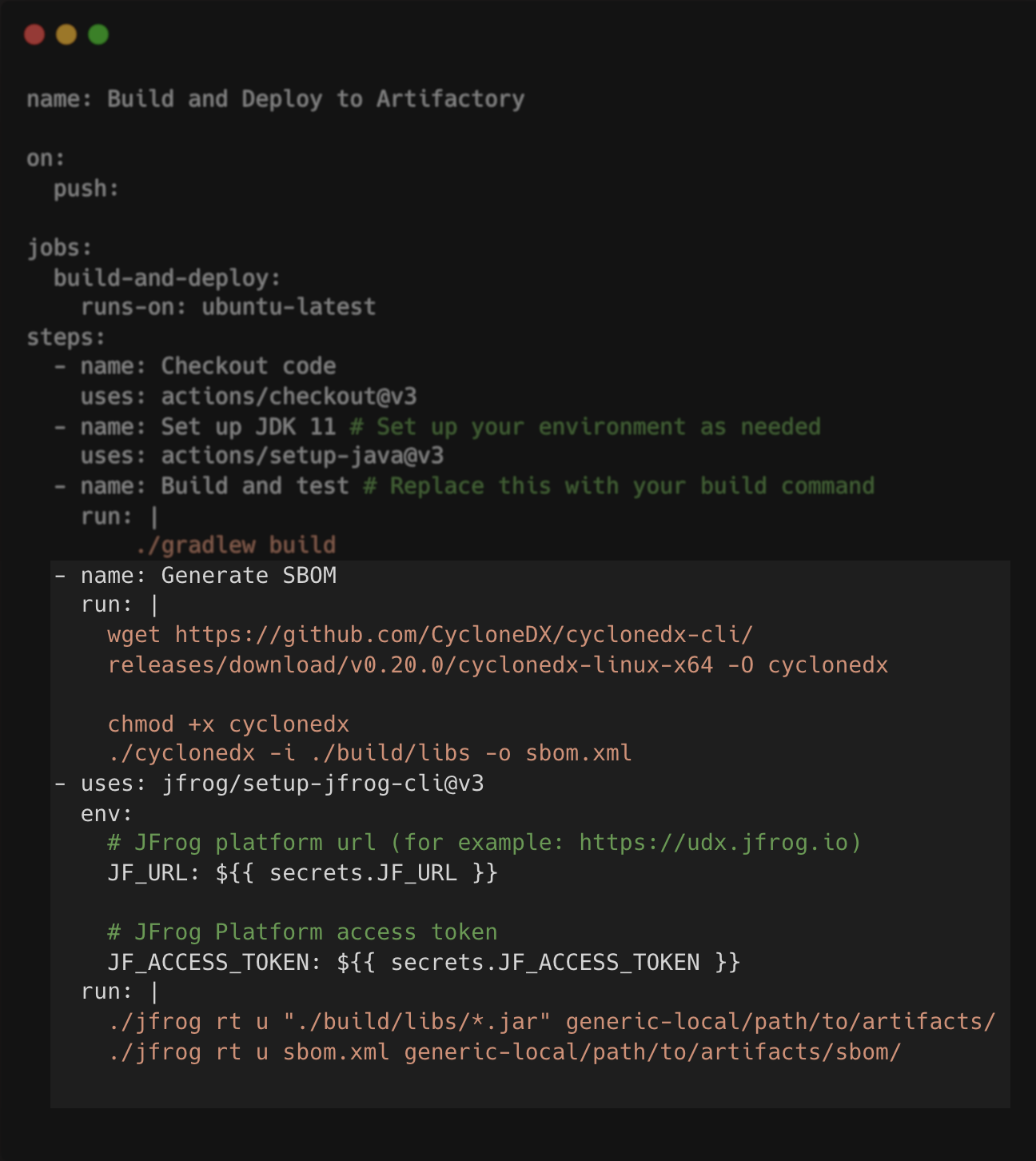
Continuous Integration Example
Implement continuous monitoring by integrating SBOMs into your software composition analysis (SCA) tools. These tools can monitor your SBOM against newly discovered vulnerabilities and alert you to any that affect your components.
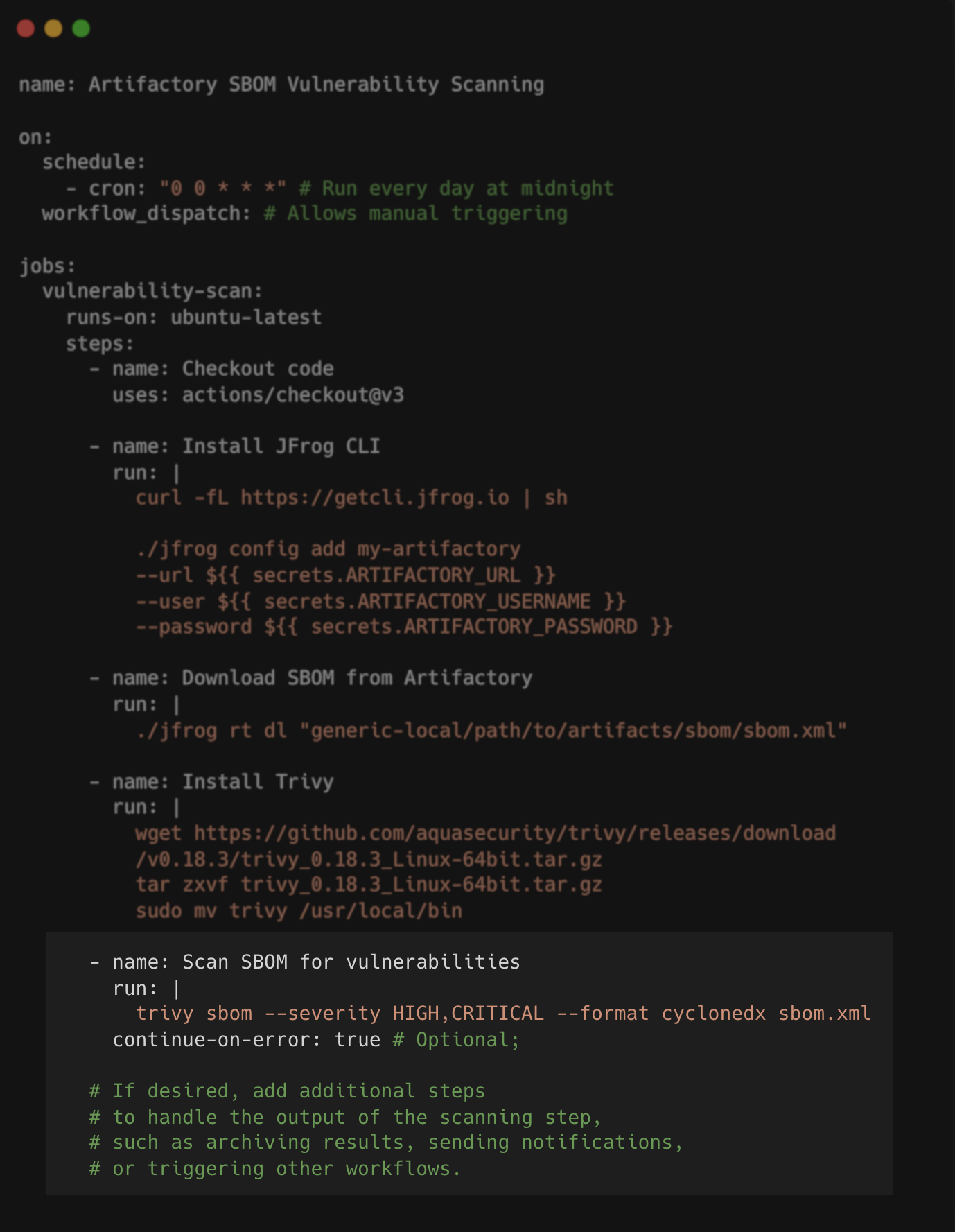
Continuous Monitoring/Scanning Example
When deploying applications, reference the SBOM or latest generated scan report to ensure that the deployed software matches the verified and compliant components listed. This can be a pre-deployment "Control Gate" that ensures compliance with internal and external regulations.

The diagram demonstrates where Control Gates in the supply chain could be integrated
- Utilize the SBOM in your incident response protocols.
- The SBOM can quickly provide information on the affected components, facilitating a faster and more effective response.
- Regularly audit your software against the SBOM to ensure ongoing compliance with licensing and security standards.
- The SBOM serves as a foundation for audits and compliance checks, streamlining the verification process for both internal audits and external regulatory requirements.
- Share your SBOM with vendors and stakeholders to enable better communication regarding dependencies and security matters.
- The transparency within SBOM helps in building trust and managing software supply chain risks more effectively.
- SBOM Generation: CycloneDX, SPDX Tools, SWID - designed to automatically generate a comprehensive inventory of software components in standardized SBOM formats.
- Software Composition Analysis (SCA): OWASP Dependency-Track, Snyk, Black Duck - scans for vulnerabilities in software dependencies, offering insights and remediation guidance, often with SBOM import capabilities.
- Package Managers: NPM, Maven, NuGet - Ecosystem-specific tools that manage software dependencies and may generate SBOM data as part of their regular operations.
- CI/CD: GitLab CI, GitHub Actions, Azure DevOps, Jenkins - workflow services that integrate with SBOM and SCA tools to provide security checks within CI/CD pipelines.
- Repository Managers: JFrog Artifactory, Sonatype Nexus - Binary repository managers that can store and serve binary resources such as artifacts and containers, often with metadata and SBOM integration features.
Talk to an Expert
Connect with our diverse group of UDX experts that can help you implement successful DevOps practices within your organization.